Chapter 8. Tools & Accessories
Complete tools inventory, accessories catalog, and procurement guidance
A successful authorization system deployment requires a comprehensive set of tools and accessories spanning development, testing, infrastructure provisioning, security assessment, monitoring, documentation, and physical deployment components. This chapter provides a complete inventory of recommended tools organized by category, along with procurement guidance, licensing considerations, and notes on open-source alternatives where applicable. The accessories inventory diagram below provides a visual overview of all tool categories, followed by detailed specification tables for each category.
8.1 Tools & Accessories Inventory Overview
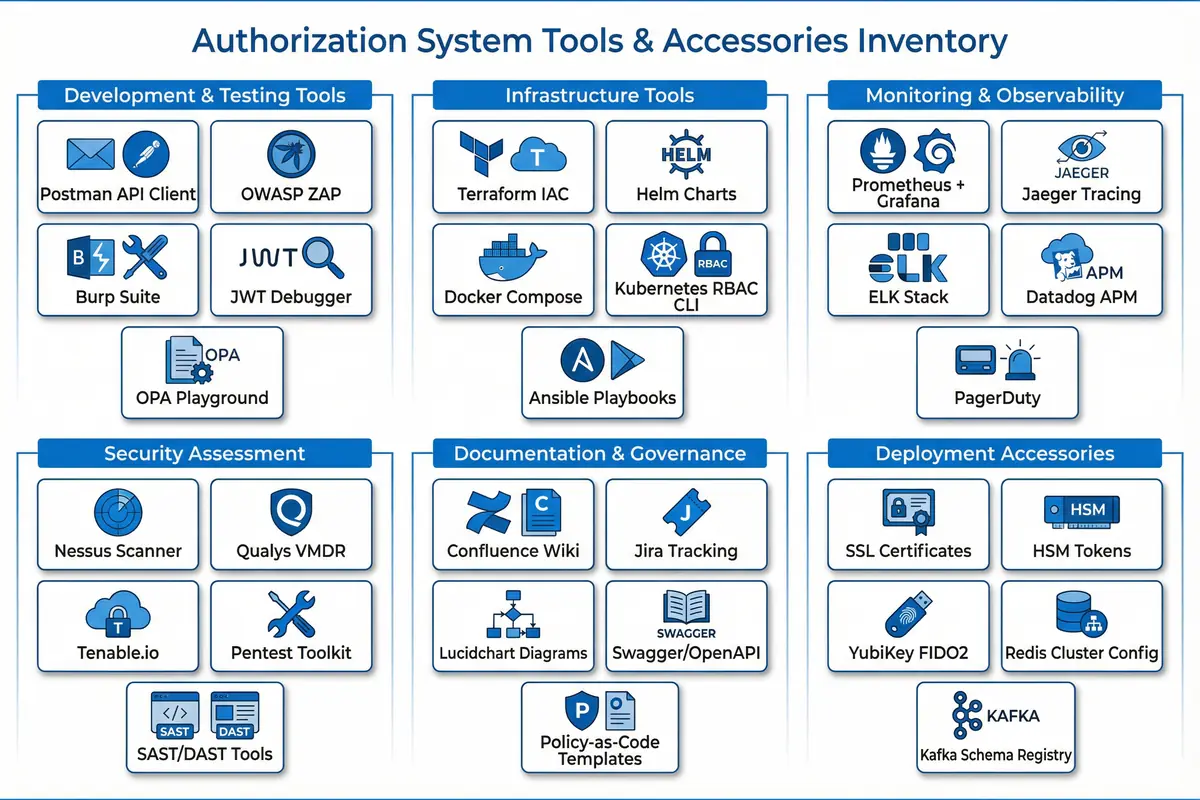
Figure 8.1: Authorization System Tools & Accessories Inventory — Complete 6-category inventory showing Development & Testing Tools, Infrastructure Tools, Monitoring & Observability, Security Assessment, Documentation & Governance, and Deployment Accessories
8.2 Development & Testing Tools
Development and testing tools are essential for validating the authorization system's behavior during implementation and ongoing maintenance. These tools enable engineers to test API endpoints, simulate attack scenarios, debug JWT tokens, and validate policy logic before deployment to production environments.
| Tool | Category | License | Primary Use | Notes |
|---|---|---|---|---|
| Postman API Client | API Testing | Freemium | Authorization API endpoint testing; collection-based regression tests | Export collections for CI/CD integration |
| OWASP ZAP | Security Testing | Open Source (Apache 2.0) | Automated API security scanning; broken access control detection | Integrate in CI/CD pipeline for pre-deployment scanning |
| Burp Suite Professional | Penetration Testing | Commercial | Manual penetration testing of authorization endpoints; IDOR testing | Required for annual penetration testing engagements |
| JWT Debugger (jwt.io) | Token Analysis | Free | Decode and validate JWT structure; verify claims and signatures | Use offline version for production tokens containing PII |
| OPA Playground | Policy Testing | Open Source (Apache 2.0) | Interactive Rego policy development and testing | Local deployment recommended for sensitive policy testing |
8.3 Infrastructure Tools
Infrastructure tools enable consistent, repeatable deployment of the authorization system components across environments. Infrastructure-as-code tools ensure that all deployments are version-controlled and auditable, while container orchestration tools provide the runtime environment for the authorization platform components.
| Tool | Category | License | Primary Use | Notes |
|---|---|---|---|---|
| Terraform | Infrastructure as Code | BSL 1.1 (OpenTofu: MPL 2.0) | Provision cloud infrastructure; manage Kubernetes clusters and databases | Use remote state with locking for team environments |
| Helm Charts | Kubernetes Packaging | Open Source (Apache 2.0) | Package and deploy authorization components to Kubernetes | Maintain separate values files per environment |
| Docker Compose | Local Development | Open Source (Apache 2.0) | Local development environment with all authorization components | Not for production use; use Kubernetes for production |
| Kubernetes RBAC CLI | K8s Management | Open Source (Apache 2.0) | Manage Kubernetes RBAC for authorization system service accounts | Apply least privilege to all service account permissions |
| Ansible Playbooks | Configuration Management | Open Source (GPL 3.0) | Automated configuration of authorization system dependencies | Idempotent playbooks; vault for secrets management |
8.4 Monitoring & Observability Tools
| Tool | Category | License | Primary Use | Key Metrics to Monitor |
|---|---|---|---|---|
| Prometheus + Grafana | Metrics & Dashboards | Open Source (Apache 2.0) | PDP latency, decision throughput, cache hit rate dashboards | pdp_decision_latency_ms, cache_hit_ratio, decisions_per_second |
| Jaeger Tracing | Distributed Tracing | Open Source (Apache 2.0) | End-to-end request tracing from PEP through PDP to resource service | Trace authorization decision path; identify latency bottlenecks |
| ELK Stack | Log Analytics | Open Source (Elastic License) | Authorization audit log indexing, search, and visualization | Audit event volume, error rates, denied access patterns |
| Datadog APM | Application Performance | Commercial SaaS | Full-stack observability for production authorization platform | Service health, dependency maps, anomaly detection |
| PagerDuty | Incident Management | Commercial SaaS | On-call routing for authorization system alerts; escalation policies | MTTR for authorization incidents; alert noise ratio |
8.5 Deployment Accessories
| Accessory | Type | Quantity | Purpose | Procurement Notes |
|---|---|---|---|---|
| SSL/TLS Certificates (Wildcard) | Digital Certificate | 1 per domain | Secure all authorization API endpoints and admin interfaces | Use internal CA for internal services; public CA for external-facing APIs |
| HSM Tokens (FIPS 140-2 Level 3) | Hardware Security Module | 2 (primary + backup) | Protect signing keys for JWT tokens and audit log hash chain | Thales Luna or AWS CloudHSM; budget $15,000–$50,000 per unit |
| YubiKey 5 NFC (FIDO2) | Hardware MFA Token | 1 per privileged admin + 20% spare | Hardware MFA for privileged station access and break-glass procedures | Yubico Enterprise; budget $50–$70 per unit; spare pool required |
| Redis Cluster Configuration | Software Configuration | 1 per environment | High-availability cache configuration for PDP Engine | Minimum 3-node cluster; Redis Enterprise for production; budget $20,000+/year |
| Kafka Schema Registry | Software Component | 1 per Kafka cluster | Schema validation and versioning for authorization audit events | Confluent Schema Registry (commercial) or Apicurio (open source) |