Chapter 5. Selection & Interfaces
Core product selection, interface specifications, and integration patterns
5.1 Core Product Introduction
The authorization system is composed of five core product modules, each addressing a distinct functional domain of the permission management lifecycle. These modules are designed to be deployed together as an integrated system, but each has well-defined interfaces that allow individual components to be replaced or upgraded independently as requirements evolve. The following product overview diagram illustrates the five core modules with their key specifications and relationships.
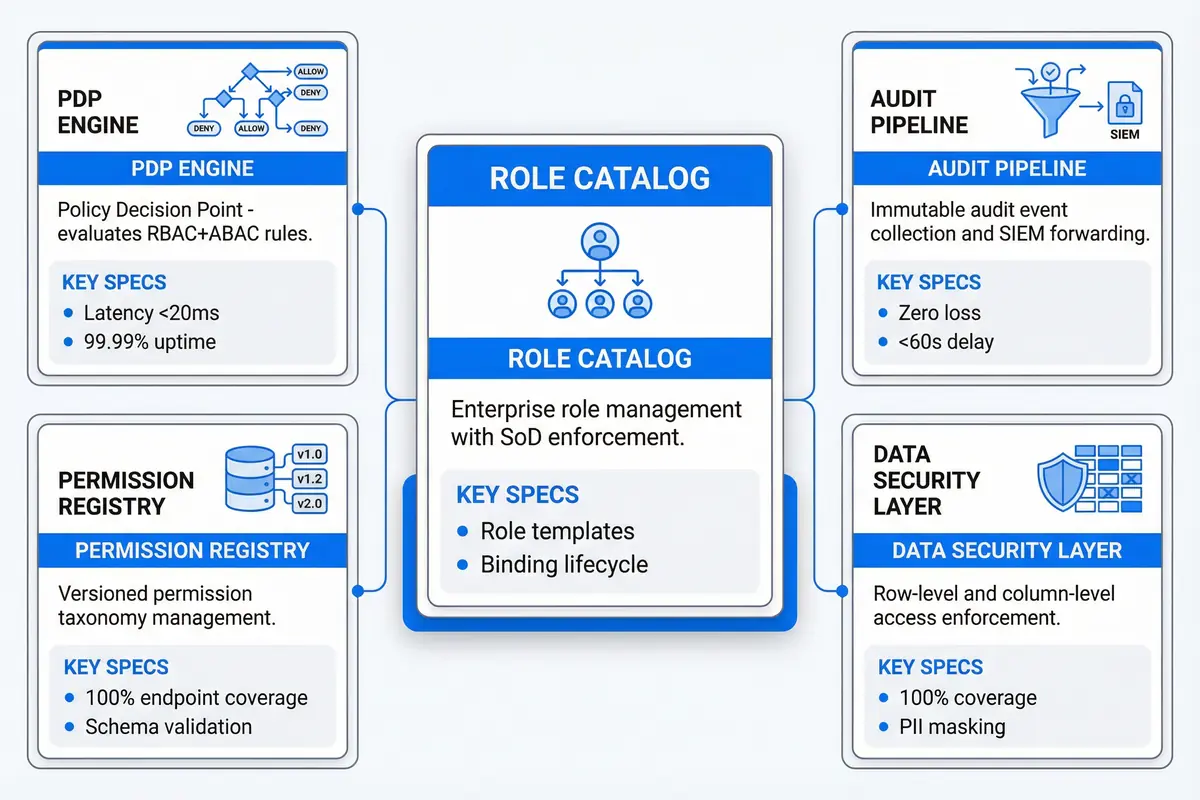
Figure 5.1: Core Product Modules — Five-card overview showing PDP Engine, Permission Registry, Role Catalog (featured), Audit Pipeline, and Data Security Layer with key specifications
| Product Module | Primary Function | Key Performance Specs | Deployment Requirements | Replacement Complexity |
|---|---|---|---|---|
| PDP Engine | Real-time authorization decision evaluation combining RBAC grants and ABAC conditions | p95 <20ms; p99 <50ms; 99.99% availability; 10k decisions/sec per instance | Minimum 2 instances for HA; Redis cache required; gRPC endpoint exposed | High — central to all enforcement; requires full regression testing |
| Permission Registry | Versioned taxonomy of all resources and operations; single source of truth for permission IDs | Schema validation <100ms; version diff <500ms; 100% endpoint coverage enforced | PostgreSQL backend; REST API; CI/CD integration for coverage gates | Medium — requires migration mapping for permission ID changes |
| Role Catalog | Enterprise role management with SoD enforcement, role templates, and binding lifecycle | Role lookup <5ms (cached); binding change propagation <60s; role count governed | PostgreSQL backend; Redis cache; event bus integration for invalidation | Medium — role migration tooling required for catalog restructuring |
| Audit Pipeline | Immutable audit event collection, schema normalization, and SIEM forwarding | Zero event loss; end-to-end delay <60s; schema completeness 100% | Kafka cluster; append-only storage (S3/WORM); SIEM connector configured | Low — pipeline can be replaced without affecting enforcement |
| Data Security Layer | Row-level and column-level access enforcement at the data access layer | Filter overhead <5ms; 100% coverage of sensitive data paths; PII masking enforced | ORM/query interceptor integration; data classification tags required | High — deeply integrated with data access patterns; requires thorough testing |
5.2 Interface Specifications and Connection Logic
The authorization system exposes a comprehensive set of interfaces organized into four categories: Identity Interfaces for provisioning and authentication integration, Management Interfaces for administrative operations, Integration Interfaces for event streaming and SIEM connectivity, and Enforcement Interfaces for real-time authorization decisions. Each interface has a defined protocol, authentication mechanism, and rate limit that must be respected by all consumers.
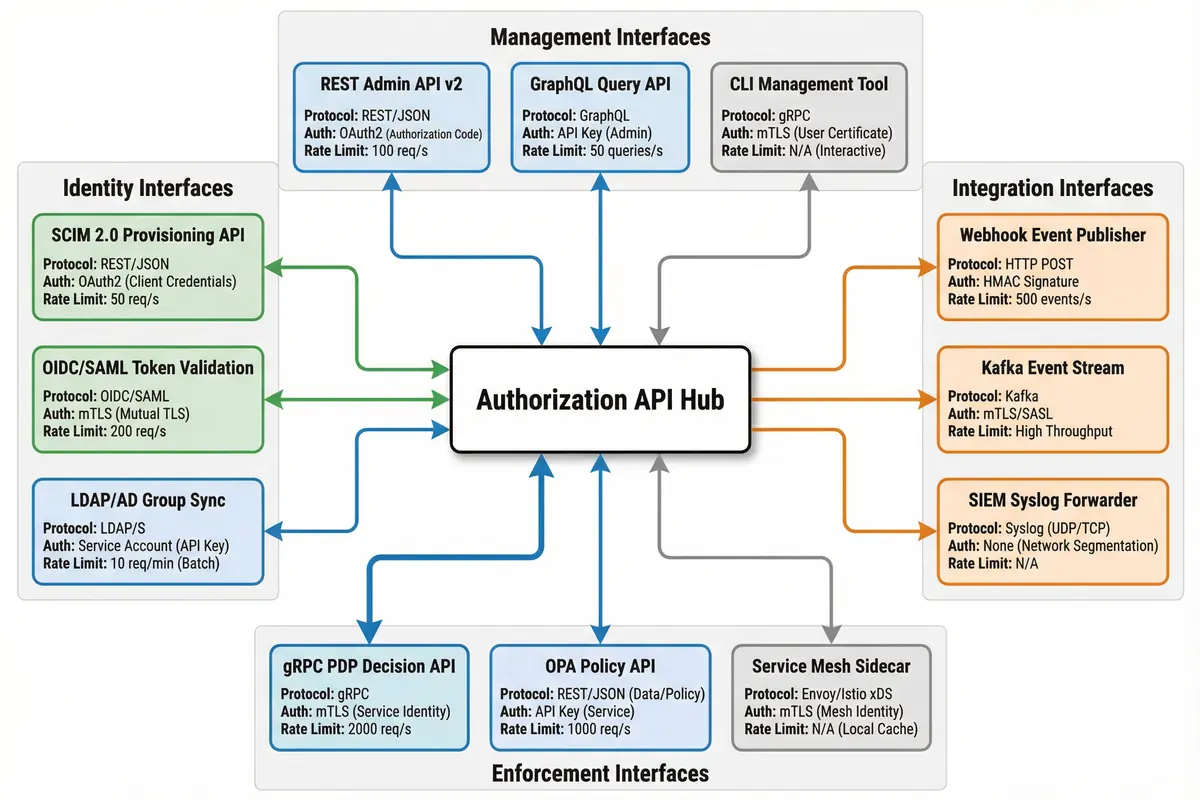
Figure 5.2: Authorization API Interface Diagram — Hub-and-spoke layout showing Identity, Management, Integration, and Enforcement interface categories with protocol, authentication method, and rate limit specifications
| Interface | Category | Protocol | Authentication | Rate Limit | Primary Use Case |
|---|---|---|---|---|---|
| SCIM 2.0 Provisioning API | Identity | REST/JSON (HTTPS) | OAuth2 Client Credentials | 50 req/s | User and group provisioning from IdP |
| OIDC/SAML Token Validation | Identity | OIDC/SAML (HTTPS) | mTLS | 200 req/s | Token introspection and claim extraction |
| LDAP/AD Group Sync | Identity | LDAPS | Service Account (API Key) | 10 req/min (batch) | Group membership synchronization |
| REST Admin API v2 | Management | REST/JSON (HTTPS) | OAuth2 Authorization Code | 100 req/s | Role management, binding administration |
| GraphQL Query API | Management | GraphQL (HTTPS) | API Key (Admin) | 50 queries/s | Flexible permission and role queries |
| CLI Management Tool | Management | gRPC | mTLS (User Certificate) | N/A (Interactive) | Operator CLI for role and policy management |
| Webhook Event Publisher | Integration | HTTP POST (HTTPS) | HMAC Signature | 500 events/s | Real-time authorization event delivery |
| Kafka Event Stream | Integration | Kafka (SASL/TLS) | mTLS/SASL | High throughput | Audit log streaming to SIEM and analytics |
| SIEM Syslog Forwarder | Integration | Syslog (UDP/TCP) | Network segmentation | N/A | Legacy SIEM integration via syslog |
| gRPC PDP Decision API | Enforcement | gRPC (mTLS) | mTLS (Service Identity) | 2000 req/s per instance | Real-time authorization decisions from PEP |
| OPA Policy API | Enforcement | REST/JSON (HTTPS) | API Key (Service) | 1000 req/s | OPA-compatible policy evaluation |
| Service Mesh Sidecar | Enforcement | Envoy/Istio xDS | mTLS (Mesh Identity) | N/A (Local Cache) | Sidecar-based enforcement in service mesh |
5.3 Core Product Functions Reference
The following comprehensive function reference table covers all major capabilities of the authorization system, organized by product module. Each function entry includes the function name, description, applicable tier, required dependencies, and the acceptance criterion that must be satisfied during deployment testing.
| Module | Function | Description | Tier | Acceptance Criterion |
|---|---|---|---|---|
| PDP Engine | RBAC Evaluation | Evaluate role-to-permission grants for a subject-action-resource tuple | Core | Correct allow/deny for all role-permission test cases |
| ABAC Condition Evaluation | Evaluate attribute-based conditions including network zone, time, and device trust | Optional | Conditions correctly restrict access when attributes don't match | |
| Obligation Generation | Return MFA step-up, approval ID, or PAM session requirements as obligations | Core | Obligations are enforced by PEP before operation proceeds | |
| Batch Decision API | Evaluate multiple subject-action-resource tuples in a single request for UI menu rendering | Core | Batch response matches individual decision results; latency <50ms for 50 items | |
| Permission Registry | Permission Registration | Register new resource types and operations with versioned IDs | Core | New permissions immediately available for role assignment |
| Coverage Validation | Validate that all API endpoints have registered permission IDs | Core | Coverage check fails CI/CD if any endpoint is unmapped | |
| Version Migration | Manage permission ID renames and removals with backward compatibility mapping | Core | Old permission IDs continue to work during migration window | |
| Role Catalog | Role Template Management | Create and manage role templates with predefined permission sets for common job functions | Core | Templates can be instantiated for new users without manual permission assignment |
| SoD Rule Enforcement | Prevent role assignments that violate separation of duties rules | Core | SoD-violating assignments are rejected with clear reason code | |
| Binding Lifecycle Management | Manage role assignment creation, modification, expiry, and revocation | Core | Expired bindings are automatically revoked; revocation propagates within 60s | |
| Audit Pipeline | Event Schema Normalization | Normalize authorization events from all enforcement points into a consistent schema | Core | All events contain required fields; schema validation passes 100% |
| Tamper-Evidence | Ensure audit logs cannot be modified or deleted after writing | Core | Append-only storage verified; hash chain integrity check passes | |
| Data Security Layer | Row-Level Filtering | Filter query results to rows matching the subject's tenant, project, or case scope | Optional | Cross-tenant row access returns empty result, not error |
| Column Masking | Mask sensitive columns (PII, secrets) for subjects without explicit data access permission | Optional | Masked fields return redacted value; unmasking requires explicit permission |