User and Role Permission Model Design Guide
A comprehensive, enterprise-grade reference for designing governable, auditable, and evolvable authorization systems across cybersecurity platforms — covering RBAC, ABAC, lifecycle governance, high-risk controls, and compliance alignment.
System Overview
A User & Role Permission Model for cybersecurity platforms standardizes "who (user/account) under which conditions (scenario/environment/time/device) can perform which operations on which resources" into a governable, auditable, and evolvable authorization system. The scope of this guide covers the control-plane of security products and security operations platforms: admin portals, API access, tenant administration, device/policy management, incident response workflows, and sensitive data including telemetry, alerts, evidence, and configuration backups.
This guide explicitly includes human users (security analysts, SOC operators, tenant admins, auditors), service accounts (integrations, collectors, automation bots), and break-glass identities for emergency recovery. The authorization system receives inputs from identity attributes (IdP claims, groups), session context (MFA state, source IP zone, device posture), resource identifiers, request method/action, and risk signals. Outputs include allow/deny decisions, reason codes, required steps such as step-up MFA or approval, and audit events.
The core value of this model is balancing business efficiency — fast, predictable access for SOC work — with security and compliance requirements including least privilege, separation of duties, immutable audit, and accountable changes. Key dependencies include SSO/IdP, MFA provider, ticketing/workflow system, SIEM/log pipeline, secrets manager, and optionally PAM for privileged sessions.
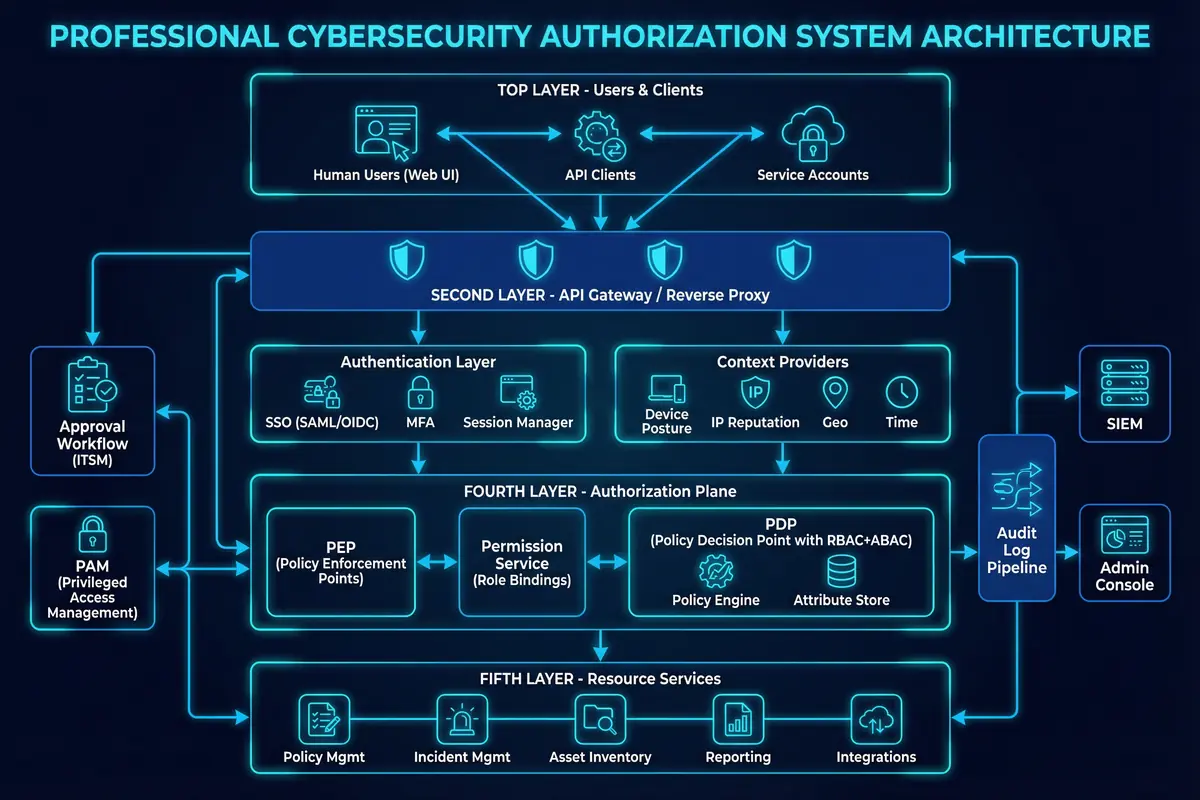
Figure 0.1: Overall Authorization Architecture — Layered diagram showing users, API gateway, authentication, authorization plane, and resource services with audit pipeline
Key Features
The authorization and governance system encompasses nine major functional domains, each addressing a critical dimension of enterprise security access control. The following diagram illustrates the functional overview map with the Authorization & Governance hub at the center, branching into specialized capability areas that together form a comprehensive permission management ecosystem.

Figure 0.2: Functional Overview Map — Mind-map showing Authorization & Governance hub with nine capability branches
| Feature | Value | Implementation | Acceptance Criteria |
|---|---|---|---|
| Role-centered RBAC with Least Privilege | Reduces ad-hoc grants; supports SoD | Role catalog, role bindings to users/groups/tenants; permission templates | Effective permissions are explainable, exportable, and testable |
| Permission Decomposition: Menu / API / Data / Operation | Prevents "UI-only security"; consistent enforcement | Every endpoint maps to operation; UI menu derived from same permission set | Disabling API permission blocks both UI and API calls |
| Privilege Tiering (Read/Operate/Admin/Privileged) | Consistent approvals and MFA rules | Every action labeled with tier and risk score | Privileged actions always trigger step-up and auditing |
| Temporary Authorization Packages with Expiry | Supports cross-team and emergency tasks without permanent drift | Time-bound grants, just-in-time (JIT) access, automatic revoke | Expired grants cannot be used; revocation is provable |
| High-Risk Action Safeguards: MFA + Workflow + Dual Control | Stops catastrophic misconfigurations and insider risk | Approval policies, two-person rule, PAM session recording | Changes cannot be applied without required approvals and recorded evidence |
| Sensitive Data Protection: Domains + Row/Column Controls (ABAC) | Minimizes exposure of PII and secrets | Data tags, domain boundaries, row filters by tenant/project/case, column masking | Exports are limited; masked fields are enforced server-side |
| Lifecycle Governance: JML + Baselines + Periodic Reviews | Keeps access aligned to current responsibilities | Provisioning pipelines, baseline roles, review schedules, drift detection | Orphan accounts and stale roles detected and remediated within SLA |
| Unified Audit Logging and Abnormal Authorization Alerting | Accountability and rapid incident investigation | Consistent audit schema, SIEM rules, anomaly detection | Audit completeness checks pass; alerts fire on defined misuse patterns |
System Performance Targets
The authorization system is designed to meet stringent performance and reliability targets that support high-throughput SOC operations without introducing latency or availability bottlenecks.
Chapter Navigation
This guide is organized into twelve comprehensive chapters, each addressing a distinct aspect of user and role permission model design for cybersecurity platforms. Navigate directly to any chapter using the cards below or the sidebar navigation.