Chapter 10. Quality & Acceptance
Quality benchmarks, acceptance criteria, and comparison between compliant and non-compliant implementations
Quality assurance for an authorization system requires a multi-dimensional approach that evaluates functional correctness, performance characteristics, security posture, and operational readiness. Unlike traditional software quality assurance, authorization system acceptance testing must specifically validate that the system correctly enforces the intended access control semantics — that permitted actions are allowed, denied actions are blocked, and the boundary between the two is precisely where the policy specifies it should be.
This chapter defines the quality benchmarks and acceptance criteria that a production-ready authorization system must meet, presents a visual comparison between compliant and non-compliant implementations, and provides a structured acceptance testing checklist that can be used as the formal gate for production deployment approval.
10.1 Quality Implementation Comparison
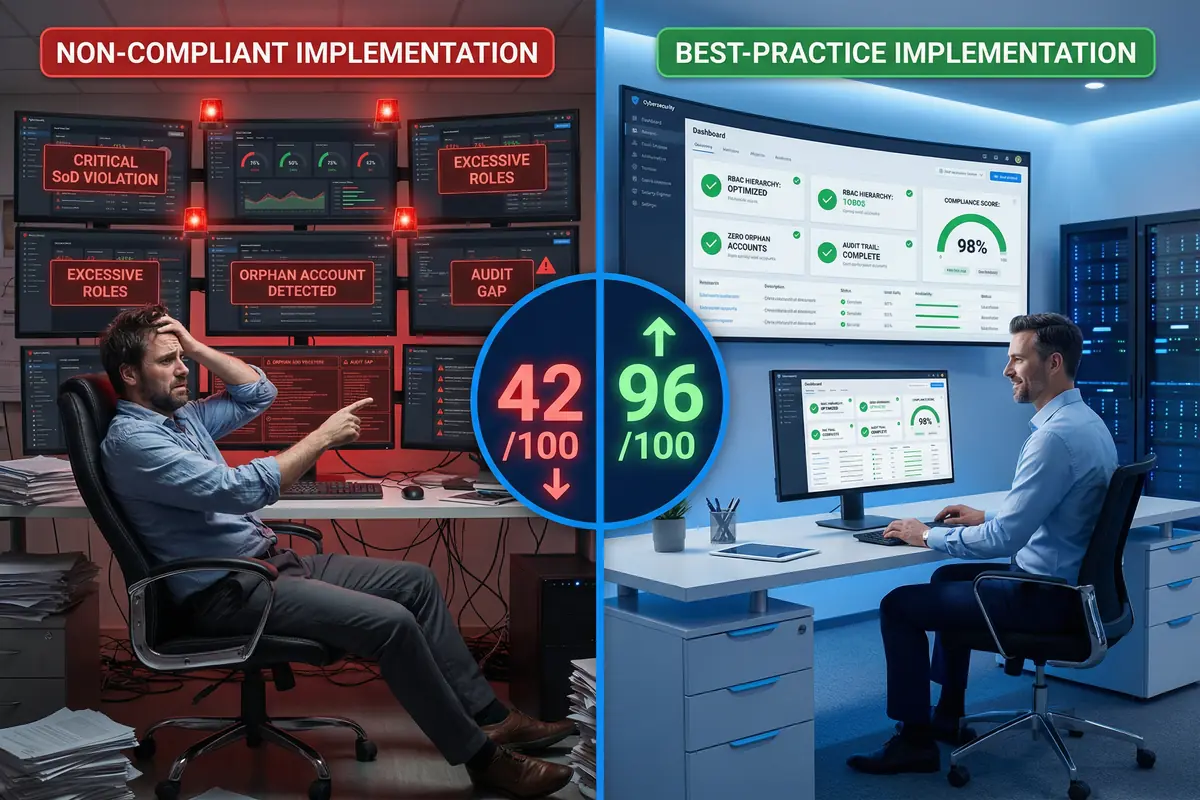
Figure 10.1: Quality Implementation Comparison — Side-by-side contrast between a non-compliant authorization implementation (score 42/100, showing SoD violations, orphan accounts, audit gaps, excessive roles) and a best-practice implementation (score 96/100, showing clean RBAC hierarchy, zero orphan accounts, complete audit trail, 98% compliance score)
10.2 Quality Benchmark Dimensions
The authorization system quality score is calculated across six dimensions, each weighted according to its criticality to security and compliance outcomes. The following table defines each dimension, its weight in the overall score, the measurement method, and the minimum acceptable threshold for production deployment.
| Quality Dimension | Weight | Measurement Method | Minimum Threshold | Target Score |
|---|---|---|---|---|
| Authorization Correctness | 30% | Automated test suite: permit/deny decision accuracy against known-good policy matrix | 99.9% accuracy (≤1 error per 1,000 decisions) | 100% accuracy |
| Performance & Latency | 20% | Load test at 2× peak load; measure p50, p95, p99 decision latency | p99 < 100ms at peak load | p99 < 50ms |
| Security Posture | 25% | Penetration test results; OWASP ZAP scan; privilege escalation test suite | Zero Critical/High findings unmitigated | Zero Critical/High/Medium findings |
| Compliance Coverage | 15% | Control mapping audit against SOC 2, ISO 27001, NIST CSF | ≥90% of required controls implemented | 100% of required controls |
| Operational Readiness | 5% | Runbook completeness review; on-call drill results; monitoring coverage | All P1 runbooks documented and tested | All runbooks documented; quarterly drills |
| Data Hygiene | 5% | Orphan account count; stale binding rate; role explosion metric | 0 orphan accounts; <5% stale bindings | 0 orphan accounts; <2% stale bindings |
10.3 Production Acceptance Criteria
The following acceptance criteria represent the minimum requirements that must be met before an authorization system deployment can be approved for production. Each criterion is binary (pass/fail) and all criteria must pass for production approval. Any failing criterion must be remediated and re-tested before deployment proceeds.
| # | Acceptance Criterion | Test Method | Pass Condition | Priority |
|---|---|---|---|---|
| AC-01 | All authorization endpoints return correct permit/deny decisions | Automated policy matrix test (≥500 test cases) | 100% pass rate | Blocker |
| AC-02 | No privilege escalation path exists in role hierarchy | Automated role hierarchy traversal test | Zero escalation paths found | Blocker |
| AC-03 | All SoD rules enforced at role assignment time | Attempt to assign conflicting role combinations | 100% of SoD violations blocked | Blocker |
| AC-04 | Audit log captures all authorization decisions | Decision sampling: compare PDP logs vs audit log | 100% decision capture rate | Blocker |
| AC-05 | PDP latency meets SLA at 2× peak load | Load test with 2× peak concurrent requests | p99 < 100ms; zero timeouts | Blocker |
| AC-06 | No Critical or High security findings unmitigated | Penetration test report review | Zero unmitigated Critical/High findings | Blocker |
| AC-07 | Failover completes within RTO | Simulate primary PDP failure; measure recovery time | Recovery < 30 seconds | High |
| AC-08 | MFA step-up enforced for all high-risk operations | Attempt high-risk operations without MFA | 100% blocked without MFA | High |
| AC-09 | Tenant isolation verified (multi-tenant deployments) | Cross-tenant access attempt test suite | Zero cross-tenant data access | High |
| AC-10 | All P1 runbooks documented and tested | Runbook completeness review + tabletop exercise | All P1 scenarios covered; exercise passed | Medium |