Chapter 6. Security & Risks
Authorization system threat model, risk matrix, and mitigation strategies
The authorization system is itself a high-value target for attackers. A compromised authorization system can grant attackers access to all resources it protects, making it essential to apply the same rigorous security controls to the authorization infrastructure as to the most sensitive resources in the organization. This chapter presents the threat model for the authorization system, analyzes the most significant risks using a likelihood-impact matrix, and provides concrete mitigation strategies for each identified risk.
The threat model follows the STRIDE framework (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege), adapted to the specific attack surfaces of authorization systems. The risk matrix plots identified threats by likelihood and impact to prioritize mitigation efforts, and each risk entry includes the attack vector, affected components, detection indicators, and recommended controls.
6.1 Authorization System Risk Matrix
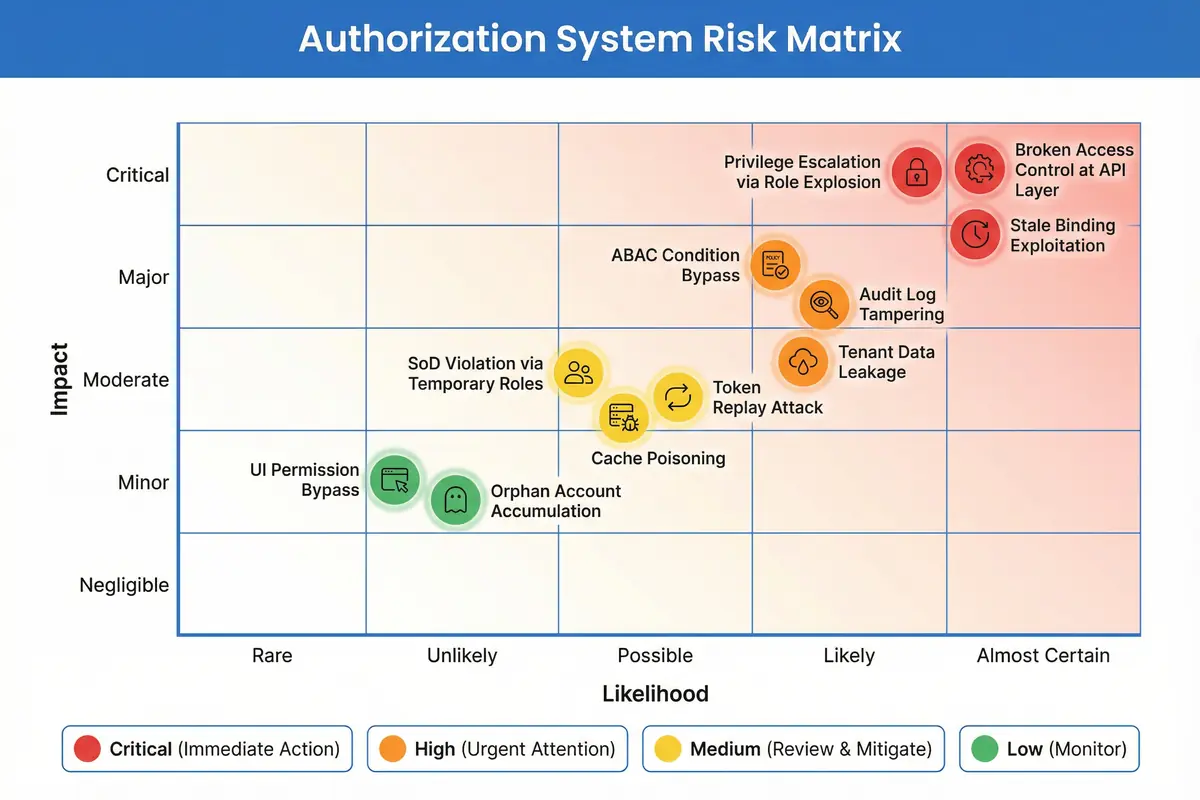
Figure 6.1: Authorization System Risk Matrix — Likelihood vs. Impact plot for 11 identified authorization risks, color-coded by severity from Critical (red) to Low (green)
| Risk | STRIDE Category | Severity | Attack Vector | Affected Components | Primary Mitigation |
|---|---|---|---|---|---|
| Privilege Escalation via Role Explosion | Elevation of Privilege | Critical | Attacker creates excessive roles to find permission gaps or exploits role hierarchy traversal | Role Catalog, PDP Engine | Role count governance; max roles per user limit; regular role explosion detection |
| Broken Access Control at API Layer | Elevation of Privilege | Critical | Direct API calls bypassing PEP; IDOR via predictable resource IDs | API Gateway, PEP, Resource Services | 100% endpoint coverage; defense-in-depth service PEP; API security testing in CI/CD |
| Stale Binding Exploitation | Elevation of Privilege | Critical | Attacker uses former employee credentials with active role bindings | Binding Manager, Identity Adapter | HR system integration; automated deprovisioning on termination; periodic access review |
| ABAC Condition Bypass | Elevation of Privilege | High | Manipulating attribute values (network zone, device trust) to satisfy conditions | PDP Engine, ABAC Library | Attribute source validation; network zone from infrastructure (not user-supplied); device trust from MDM |
| Audit Log Tampering | Tampering / Repudiation | High | Attacker with storage access modifies or deletes audit records to cover tracks | Audit Pipeline, Storage | Append-only storage; hash chain integrity; write-once S3 bucket policies; SIEM real-time forwarding |
| Tenant Data Leakage | Information Disclosure | High | Cross-tenant data access via missing row-level filters or API response leakage | Data Security Layer, Resource Services | Row-level tenant_id filter at data layer; API response validation; cross-tenant penetration testing |
| SoD Violation via Temporary Roles | Elevation of Privilege | Medium | Attacker requests temporary role that, combined with existing roles, violates SoD | Role Catalog, Binding Manager | SoD validation includes temporary and JIT roles; approval required for SoD-adjacent assignments |
| Token Replay Attack | Spoofing | Medium | Stolen JWT used to impersonate user; long-lived tokens increase exposure window | Session Manager, PEP | Short token TTL (<15 min); token binding to device fingerprint; anomaly detection on token reuse |
| Cache Poisoning | Tampering | Medium | Attacker with Redis access injects false permission grants into PDP cache | PDP Engine, Redis Cache | Redis auth and TLS; cache namespace isolation; integrity check on cache reads for sensitive decisions |
| UI Permission Bypass | Elevation of Privilege | Low | Attacker manipulates client-side permission checks to access hidden UI elements | Frontend, API Gateway | Server-side enforcement is authoritative; UI checks are cosmetic only; API always validates |
| Orphan Account Accumulation | Elevation of Privilege | Low | Accounts of departed employees remain active and are exploited by insiders or attackers | Identity Adapter, Binding Manager | Nightly HR reconciliation; orphan account alert within 24h; automatic suspension after 48h |
6.2 Defense-in-Depth Control Framework
Effective authorization security requires controls at multiple layers, ensuring that no single failure can result in a complete security breach. The defense-in-depth framework for authorization systems organizes controls into four layers: Preventive controls that stop attacks before they succeed, Detective controls that identify attacks in progress or after the fact, Corrective controls that limit damage and restore normal operation, and Deterrent controls that reduce attacker motivation through accountability mechanisms.
| Control Layer | Control | Implementation | Effectiveness |
|---|---|---|---|
| Preventive | Least Privilege Enforcement | Role templates with minimum necessary permissions; regular permission pruning | Reduces blast radius of compromised accounts |
| SoD Rule Engine | Automated SoD validation on all role assignments including temporary and JIT | Prevents insider fraud through conflicting role combinations | |
| MFA Obligation for High-Risk Actions | PDP returns MFA step-up obligation for sensitive operations; PEP enforces before proceeding | Prevents token theft from enabling high-risk actions without physical MFA | |
| Permission Coverage Gates | CI/CD gate blocks deployment of uncovered endpoints | Eliminates hidden endpoints that bypass authorization | |
| Detective | Authorization Anomaly Detection | UEBA baseline + streaming analytics on audit log; alert on behavioral deviations | Detects compromised accounts and insider threats within 60 seconds |
| Periodic Access Review | Quarterly review of all role bindings; automated stale/orphan detection | Identifies and removes excessive permissions accumulated over time | |
| Audit Log Integrity Monitoring | Hash chain verification; alert on gap or modification detection | Detects tampering with audit evidence | |
| Corrective | Automated Revocation | Webhook from HR/ITSM triggers immediate binding revocation on termination or incident | Limits exposure window for compromised or departed users |
| Break-Glass Procedure | Emergency access with full audit trail; mandatory post-incident review | Enables rapid response while maintaining accountability | |
| Deterrent | PAM Session Recording | All privileged sessions recorded with keystroke and screen capture | Deters insider abuse through accountability awareness |
| Immutable Audit Trail | Append-only storage; SIEM forwarding; legal hold capability | Supports forensic investigation and regulatory compliance |